Managed Kubernetes pricing benchmark
TL;DR: Google Cloud has the most attractive pricing for Managed Kubernetes (based on March 2020 price lists). Most organisations that consider modernising their infrastructure and app stack, are moving to…
TL;DR: Google Cloud has the most attractive pricing for Managed Kubernetes (based on March 2020 price lists). Most organisations that consider modernising their infrastructure and app stack, are moving to…
With increasing share of remote work, question of the right VPN protocol comes up more frequently. The “new” kind on the block is Wireguard. Source: https://www.ckn.io/blog/2017/11/14/wireguard-vpn-typical-setup/ Benchmark values speak a…
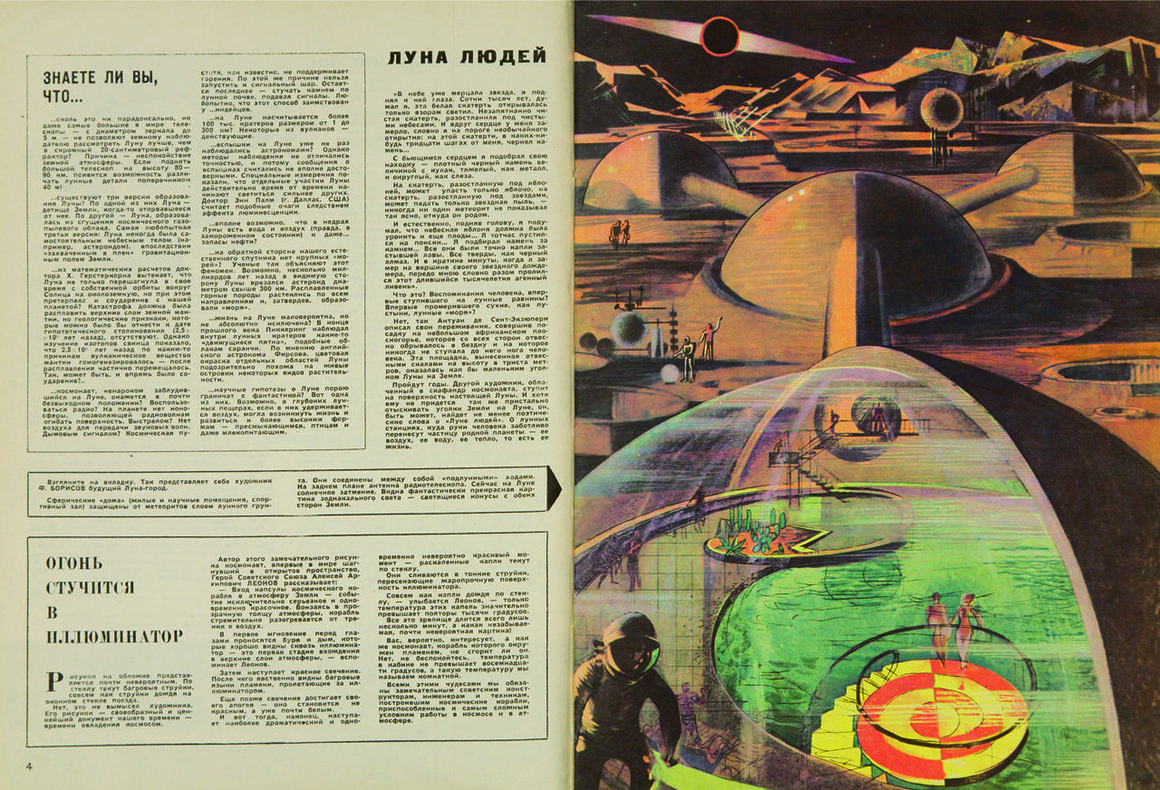
Intriguing to see how Soviets have imagined life in outer space. Topics popular in the 1960s and 1980s are now relevant again—ecology, alternative energy, reasonable consumption, overpopulation, and waste recycling.…

Searching for a good argument that we might *not* be living in a Simulation? Neil deGrasse Tyson have finally found one. Love it!
Enjoyed reading a story from Google Site Reliability Engineering about the way they trace problems. At Google scale, million-to-one chances happen all the time All incidents should be novel.

Data centers are the backbone of the digital world, they are responsible for 1% of world’s electricity use. Good news though – all hyperscalers (Google, Amazon, Microsoft) have worked hard…

Rahul Vohra (founder of Superhuman, my favourite email app) spoke about how he designed an enterprise application based on 7 primary game design principles to make it fun, rewarding and…

Art knows no limits… Beautiful examples of CSS perfection to draw famous images. Fun fact – it looks different depending on the browser you choose 🙂 Hint: Chrome and Safari…
In case you want to share photos and videos on internet, but don’t want face recognition engines to identify you, there might be an interesting solution – a digital cloaking…

The good old times, the winning quality of antivirus solution depended on how fast would they find out about a new threat, then add its fingerprint to the signature files…